Stuxnet Worm targets UCEM Headquarters
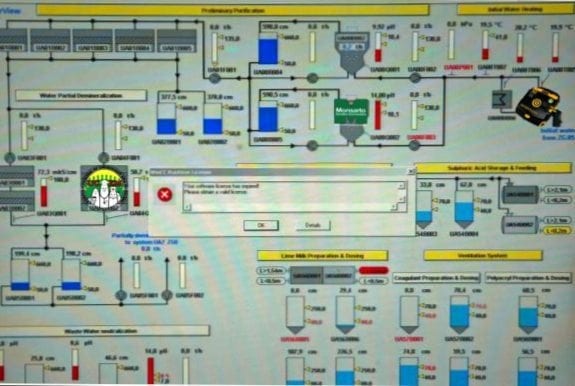
Software engineers working on the Utopian Waiting Room Medicine Conference at the Symantec Health Institute of Technology have confirmed slugtrails of the Stuxnet worm on several of the UCEM servers. Whilst initial reports suggest that US and Mossad agents might be using the worm to infiltrate the Siemens SCADA Management System of the Bushehr Nuclear Reactor in Iran (1), Professor Inglebert Struvite Staghorn of UCEM is concerned that a far more sinister motive, aimed at disrupting operations at Emergency Department Waiting Rooms is more likely.
Most of the computers in our Emergency Departments have been donated to us from Iran. Like Iran, we also use Windows 2.0 and would therefore be extremely vulnerable to any form of Cyber attack targeting this operating system…
Professor Staghorn
Microsoft has released a Patch, which addresses the ‘zero day vulnerability’ security hole. The patch (Version 9,568,964,286.2) is available on C-60 Cassette and Floppy Disk, and should prevent redistribution of the worm for the next 5 minutes, by crashing the Windows Operating System for hours.
Despite the worms formidable design in penetrating the WinCC software firewall using compromised Security Certificates (2), Professor Harry Stickler, Chair of Pedantry at the UCEM Council Executive, does not feel the worm has yet been activated.
It is clear that we have NOT yet seen any compromise to our systems, through the activation of the worm. If the worm were activated we would expect to see…
Professor Harry Stickler
- Long Emergency Department waiting times, preventing us from meeting our 4-minute rule targets
- Access block from our Waiting Rooms into the main Emergency Departments
- Poor performance of our Emergency Triage Software
- An inability to view radiological images on SUXS (Sonographic Ultrasound and X-Ray Software)
- An inability to download X-rated material from YourTube and BookFace
Software engineers are also sceptical of the depth of penetration of the Stuxnet Worm. The Stuxnet Worm was designed by an advanced, as yet unidentified, third party, with the intention of maliciously taking over large operating systems. Despite the Worm’s status as a ‘Cyber Superweapon’, the creators of the worm failed to identify 2 defensive features of the UCEM Health Information Network. Firstly, all of UCEM’s computers are incapable of propagating the worm, as they do not accept USB memory sticks, key drives or 240 volts.
Secondly, the worm is designed to infiltrate the newest generation of 21st Century Browsers, of which Netscape Navigator 3.0 is not one.
The College President, Sir Hubert Ignatius Thompson III has remained un-alarmed by the recent security threat, and issued a statement yesterday afternoon.
The thought that a driven and determined third party, with advanced organizational skills and financial resources has finally taken action, infiltrated our Emergency Department to undermine its current modus operandi, frankly does not scare me. Quite in the contrary, I have looked forward to it for quite some time. This whole place could do with a good de-worming.
References
- The Economist: “A cyber-missile aimed at Iran?” Sept 26, 2010
- The Christian Science Monitor – CSMonitor.com
- Wild Security Inc [Reference PDF]
- Knowledge Brings Fear: Stuxnet: targeting the iranian enrichment centrifuges in Natanz?
BA MA (Oxon) MBChB (Edin) FACEM FFSEM. Emergency physician, Sir Charles Gairdner Hospital. Passion for rugby; medical history; medical education; and asynchronous learning #FOAMed evangelist. Co-founder and CTO of Life in the Fast lane | On Call: Principles and Protocol 4e| Eponyms | Books |